Next Generation Cloud Security: Real-Time CSPM
Identify, prioritize, and remediate the most critical cloud security risks in real-time
Real-Time CSPM Data SheetUncover Hidden Cloud Security Risks
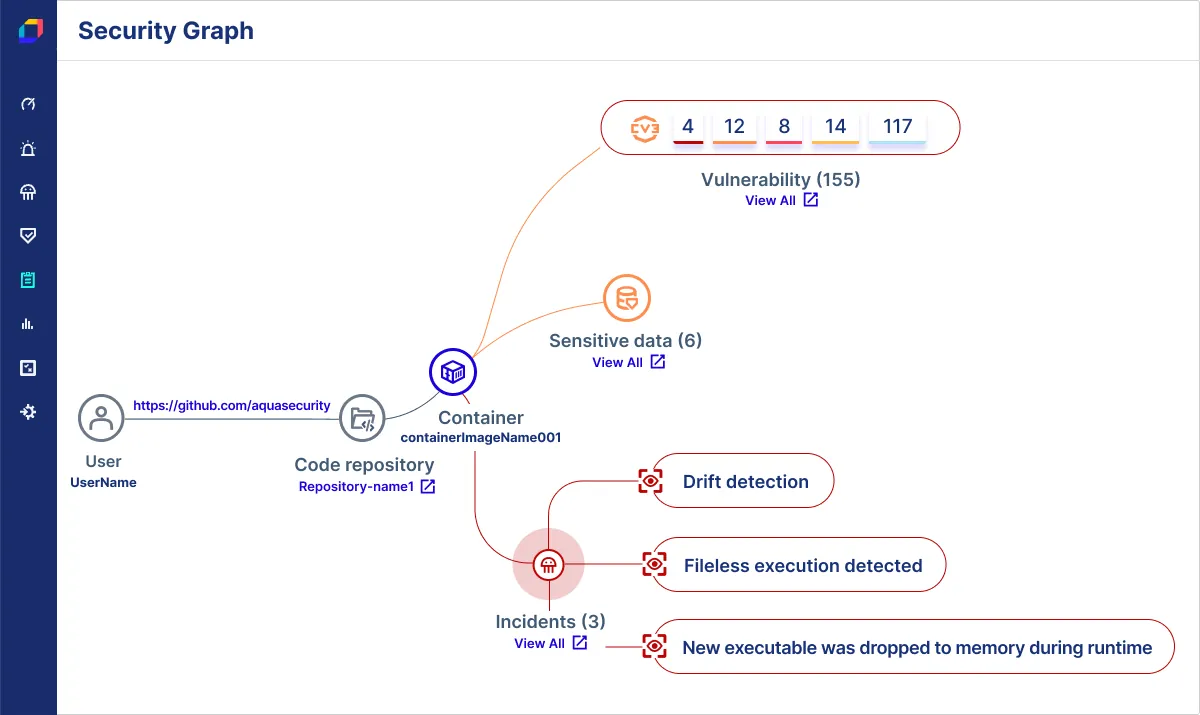
Gain a complete and prioritized view of your cloud security risk in real-time. By combining agentless scanning with real-time in-workload visibility, Aqua delivers deeper insights, helps you better control your cloud spend, and uncovers threats that evade snapshot-based detection including in-memory malware and unknown exploits like zero-days.
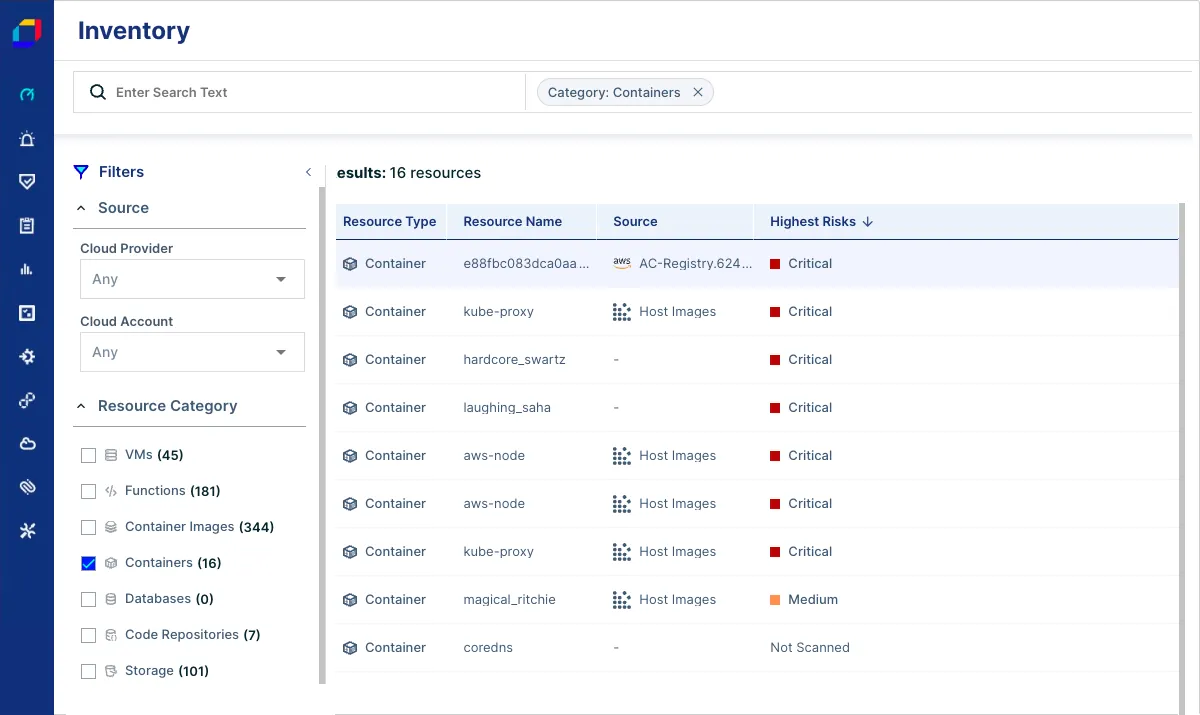
Discover all Your Cloud Resources
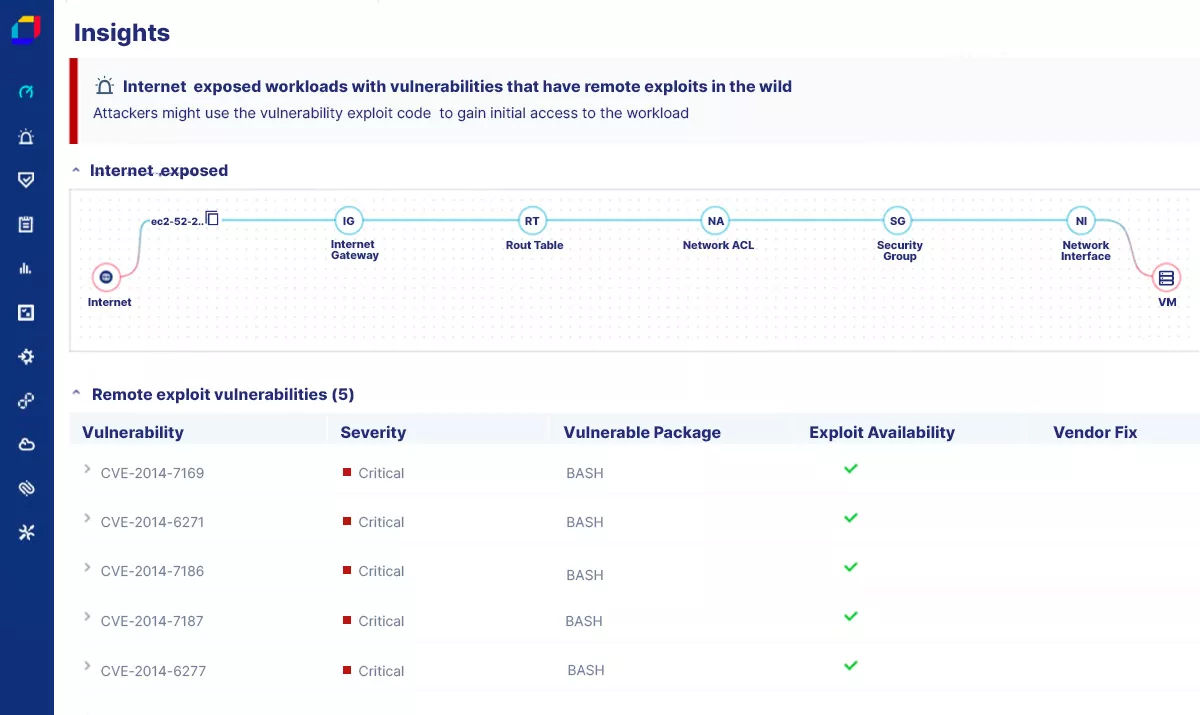
Connect your cloud accounts through cloud provider APIs, discover all existing cloud resources, and map out your entire environment. Further drill down into specific resources or risks across your VMs, containers, serverless functions, and Kubernetes clusters running in AWS, Azure, and Google Cloud. Easily see, search, and drill down into specific cloud resources or risks with the unified cloud inventory.


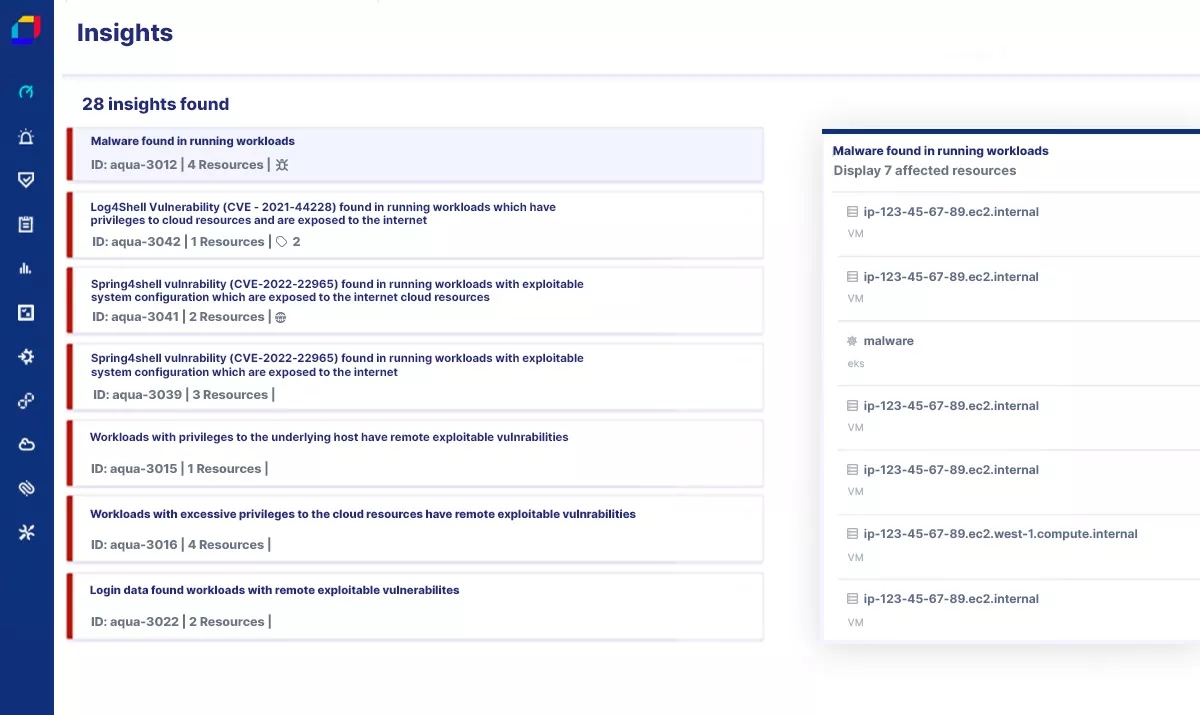
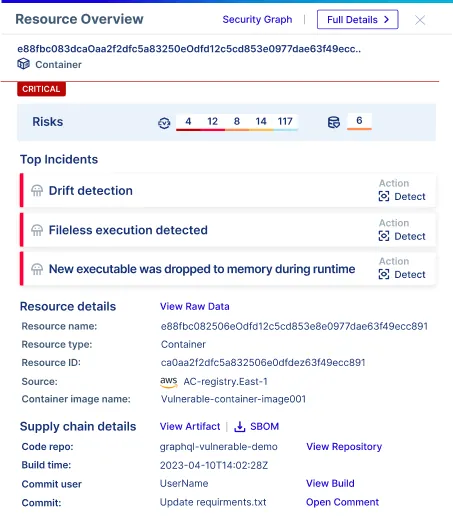
Determine Risk Exposure and Prioritize Risks
Understand your complete risk exposure to complex vulnerabilities with contextualized risk scoring and match correlated findings across multi-cloud environments. With smarter, real-time insights, you can determine root cause faster and eliminate noise by aggregating duplicates across findings for higher-fidelity risk detection.
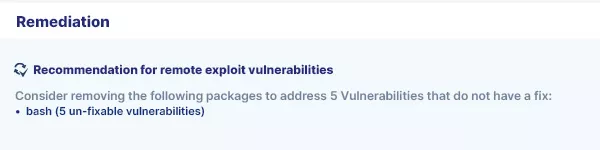
Remediate Critical Issues Fast
Focus solely on fixing high-priority issues to make a meaningful impact on risk reduction without wasting time sifting through low-level alerts or duplicate tickets. Leverage built-in expert guidance for smarter risk management and extend capabilities to connect issues found in the cloud to their respective code in repositories, identifying owners and remediating issues faster.
Complete Cloud Security
Go beyond point-in-time scanning by offering the flexibility to choose the right level of security for a given workload, making it more cost-effective while still delivering the most complete view of your cloud security risk—all from a single platform.
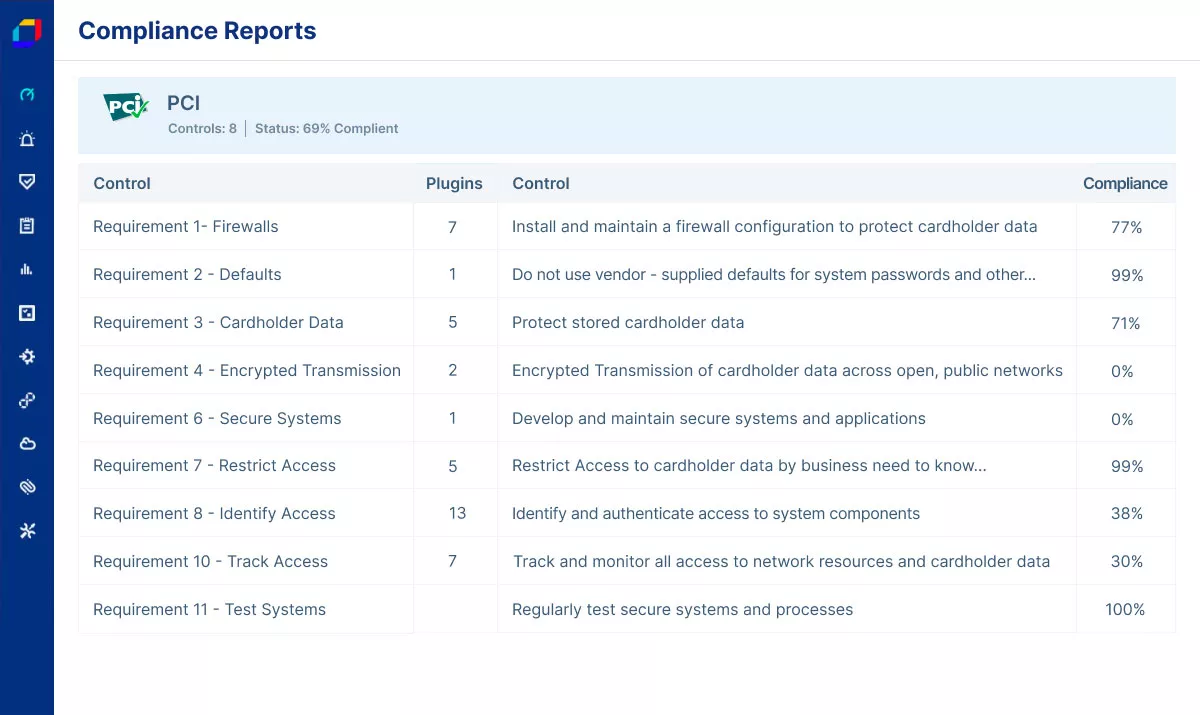
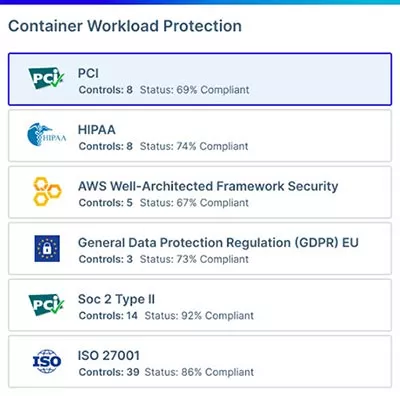
Confidently Prove Compliance
Easily achieve and maintain compliance across your multi-cloud environment with built-in reports for more than 30 common regulatory standards, including NIST, PCI, HIPAA, and GDPR. Aqua automates cloud compliance by continuously auditing your cloud accounts for drifts and potential violations across dozens of industry standards and compliance best practices.
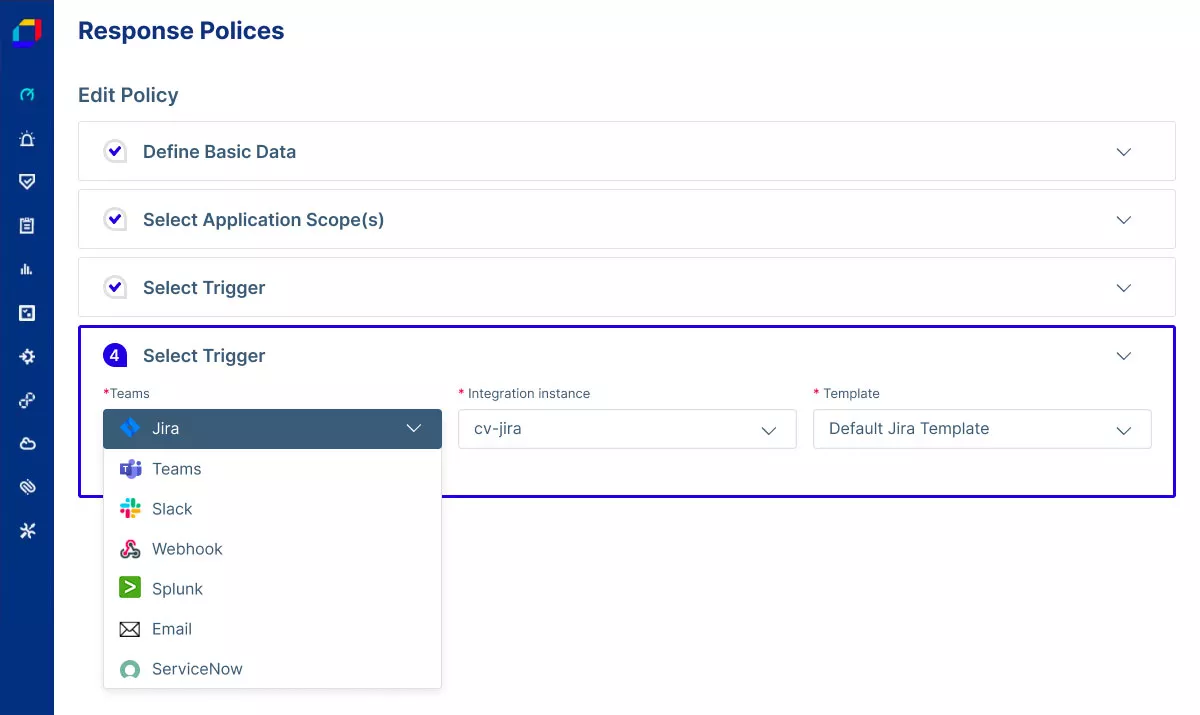
Take Action With Response Policies
Automatically trigger actions based on insights and risks discovered and update ticketing systems or post to instant messaging platforms to notify the relevant teams.